There are some methods through which we can suppress UAC prompts when virtualizing using
App-V 5.0. You can try the below methods which ever suits your need.
1. SET __COMPAT_LAYER:
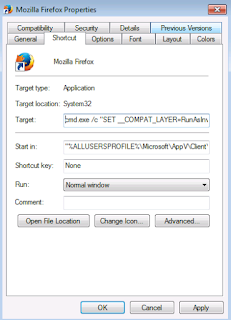
Edit the sequenced shortcut and add the below command.
cmd.exe /c “SET __COMPAT_LAYER=RunAsInvoker & START Appname.exe”
Select the required compatibility mode.In this example we have used RunAsInvoker.
Click Next.
App-V 5.0. You can try the below methods which ever suits your need.
1. SET __COMPAT_LAYER:
Edit the sequenced shortcut and add the below command.
cmd.exe /c “SET __COMPAT_LAYER=RunAsInvoker & START Appname.exe”
Note: There is a space in between SET and __COMPAT_LAYER. If you didn't leave any space it will throw an error.
"SET' is not recognized as an internal or external command.
2. Registry Method:
Right click on the shortcut and select properties-compatibility-privilege level- run as admin-apply. This will create a registry entry in the HKCU\HKLM based upon User/Machine selection.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsNT\CurrentVersion\AppCompatFlags\Layers (or)
HKEY_Current_User\SOFTWARE\Microsoft\WindowsNT\CurrentVersion\AppCompatFlags\Layers
Export the registry key and add it in the deployment config file and register it in the local machine.
NOTE: Enable script execution prior to adding the virtual package.
Set-AppVClientConfiguration –EnablePackageScripts 1
3. SHIMS:
Using Application compatibility toolkit, we can create shims to suppress the UAC prompt for an application.Install the ACT tool first and open the 32 bit compatibility administrator (since we are going to create shim for a 32 bit application).
Click on New Database - Create new- Application fix.
Select the required compatibility mode.In this example we have used RunAsInvoker.
Click Next.
Click finish to create the .sdb file.After creating open the package in the sequencer machine to add this .sdb file under scripts folder using package editor.
Save the package.Now edit the deployment config.xml file and add the script to trigger the shim database installation.
NOTE: Enable script execution prior to adding the virtual package.
Set-AppVClientConfiguration –EnablePackageScripts 1
4. Manifest File:( I usually go with this only at the worst case if none of the above methods helped me)
Usually developers create a manifest file which tells the executable as how to request the execution.
There are two types of manifest file. They are Internal/External manifest file.
Check this link - http://blogs.msdn.com/b/nikhiln/archive/2007/04/19/embed-a-manifest-to-make-an-application-elevate-in-vista.aspx
If the application has an external manifest file then it is easy to edit it and suppress the UAC prompt.
Usually external manifest will have the same executable name ending with .manifest.
We can edit the file using notepad and change the requestedExecutionLevel from "requireAdministrator" to "asInvoker" or remove the requestedExecutionLevel tag completely.By this way we can easily suppress UAC.
If there is no external manifest file seen, then it will be an embedded one within the executable. Use Resource hacker or PEExplorer tool to open up the executable. After opening you can see the requestedExecutionLevel tag in the manifest. In the example below I used Resource hacker tool to open the shortcut exe.
Change the level to "asInvoker" or you can completely remove the requestedExecutionLevel tag and compile it and save. After doing these steps manually,test once. Now your application should work fine without any UAC prompt.
If there is no external manifest file or embedded one, then you can create a new external manifest file with the same name as the executable ending with .manifest.
For example, if the main executable name is abc.exe, then the external manifest file name should be abc.exe.manifest and should be kept in the same folder. Edit the abc.exe.manifest file and create the <requestedExecutionLevel> with asInvoker as mentioned earlier.
NOTE: From vista or above if the .exe already has embedded manifest, then the external manifest will be ignored and embedded manifest is used. (This is opposite from XP case. on XP, external manifest is used and internal is ignored.)
5. SET__COMPAT_LAYER Environment Variable:
This is pretty old way. During monitoring with the sequencer, open up a elevated CMD and type in the below command.
setx __COMPAT_LAYER RunAsInvoker /m
setx = creates or modifies environment variables.
__COMPAT_LAYER = Variable.
RunAsInvoker = value.
/m = specifies that variable should be set for system wide(HKLM)
This creates an environmental variable in the package. In the configuration phase edit the shortcut and add c:\windows\system32\cmd.exe /c "START abc.exe" or c:\windows\system32\cmd.exe /c START "" abc.exe.
After publishing, the shortcut will look like this. When launching, it will open up CMD which will have the environment variable loaded inside and then start the main exe. Now the shortcut will work without UAC.
Thanks to Dan Gough and other App-V MVP's for providing different solutions which helped me to write up this blog.














This is a nice post. Thanks for sharing with us.
ReplyDeletesccm application packaging
ie11 updates windows 7
sccm bandwidth
Thanks for your valuable comment :)
DeleteQuestion here... And I maybe crazy but I swear where we have an application where this works.
ReplyDeleteI've sequenced the AppCompatFlags\Layers key in the package and it works. But... I may have one caveat there. The programs where it works for, are 'child' programs to the main application. I suspect if you try and sequence the AppCompatFlags\Layers key into your application then the virtual environment won't be loaded for that first launch and it will run as your 'native' environment without those keys... However, if you go into the bubble first and launch your programs with your bubble containing those keys, I believe it does 'AppCompat' your exe
@Trentent,
DeleteI will test your scenario and update you very soon.
We use this trick for "Phillips PACS Intellispace" with the 'Orthoview' plugin. If you try and launch this program on a server platform it fails with an error message that it only works for desktops, but setting the WINXP3 AppCompat flag in the registry in the package and it launches without complaint.
DeleteOrthoview, in this scenario, is only ever launched as a child process to the Phillips PACS application.
@Trentent,
DeleteI tested your scenario. I had an application which asked for UAC. Sequenced it and added the runasinvoker in the AppCompatFlags\Layers in HKLM during monitoring phase. Launched it in the client and see that it asks for UAC(so it wasn't looking for the keys). Opened the virtual CMD using /appvve: and launched the shortcut from here. Now it works fine without any UAC prompt.
Thanks for pointing this out. I will update the blog.
Limited users cannot even start Task Manager with group policy controlled UAC settings. The RunAsInvoker value worked well in Windows 7 (also for regedit, mmc and such), but does no longer function in Windows 10. I cannot offer using a cmd prompt to my users or clutter their desktops with shortcuts to workaround this. So is this to be considered a bug, did the necessary value change, is this just another "security fix" or is the mistake in my implementation?
ReplyDelete